Ransomware Threat Protection: A Comprehensive Guide
Understanding Ransomware Attacks
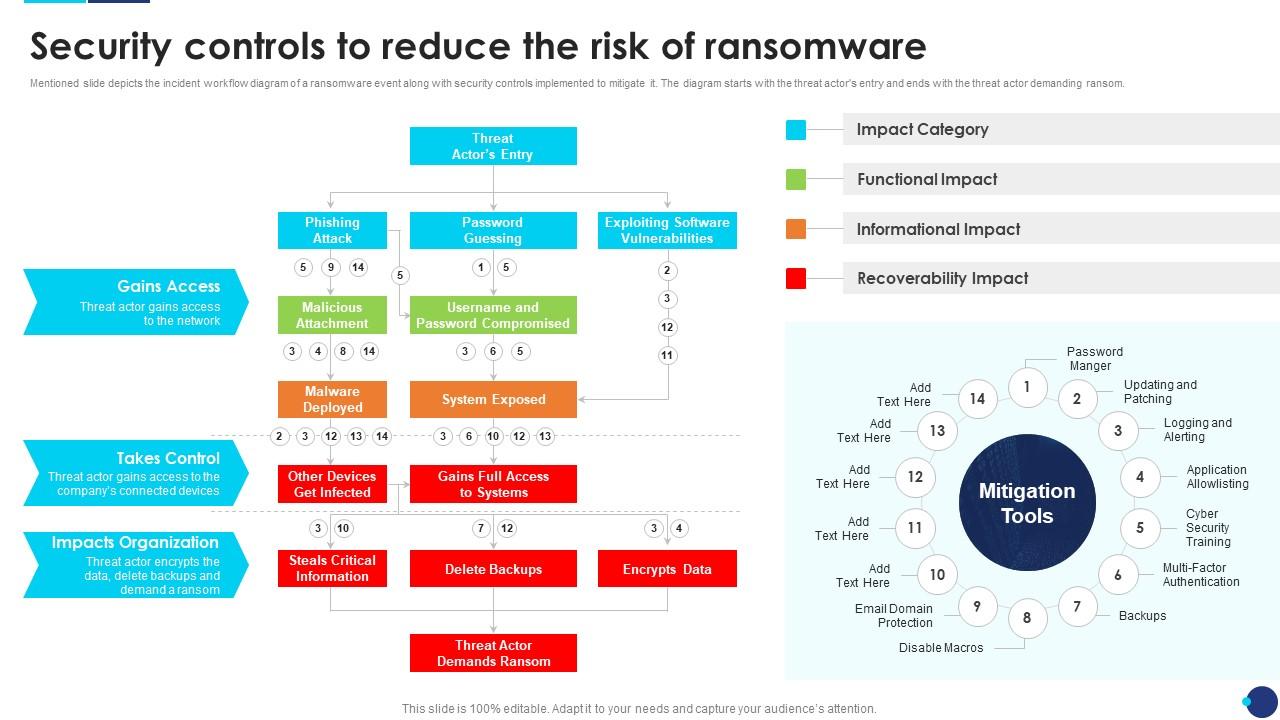
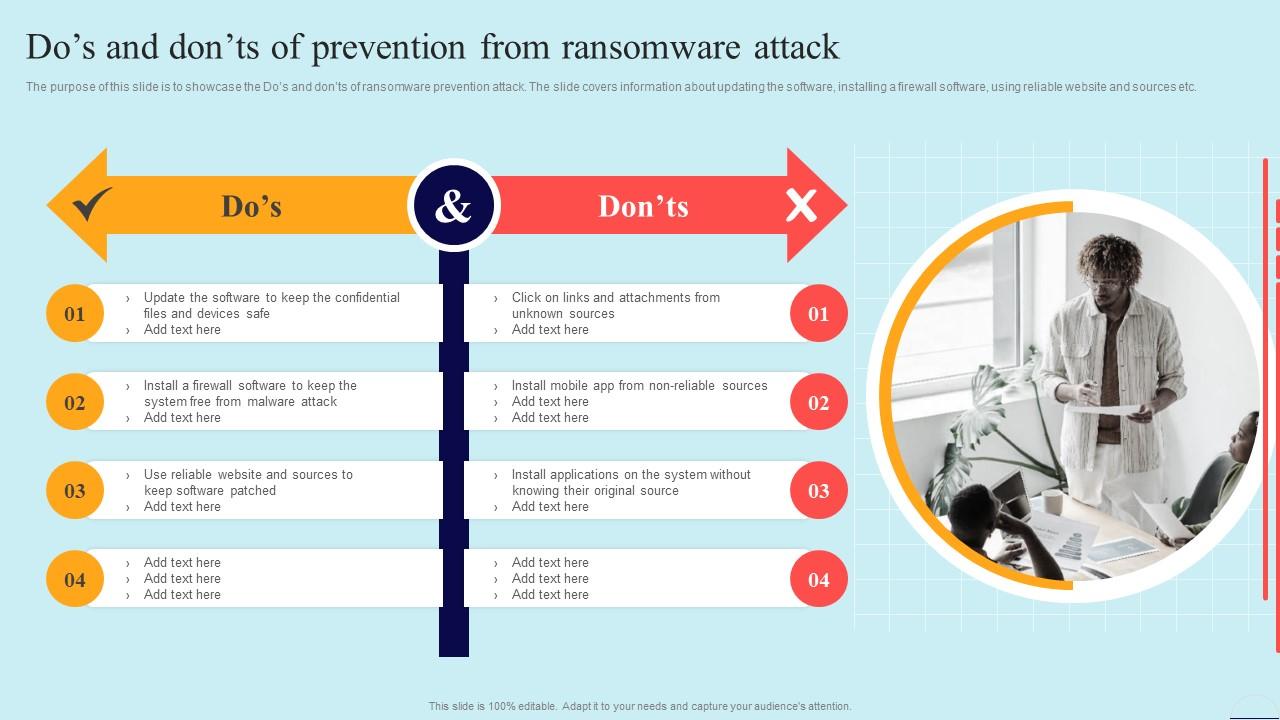
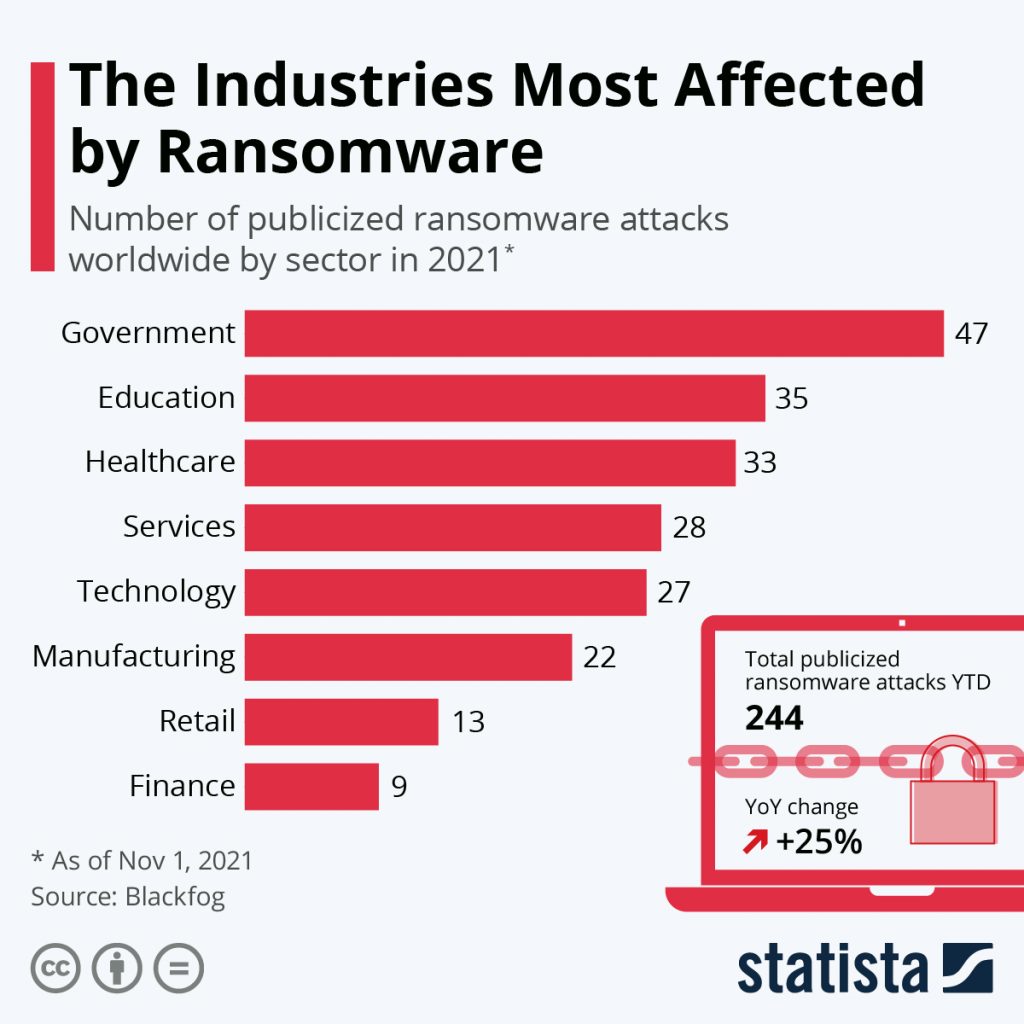
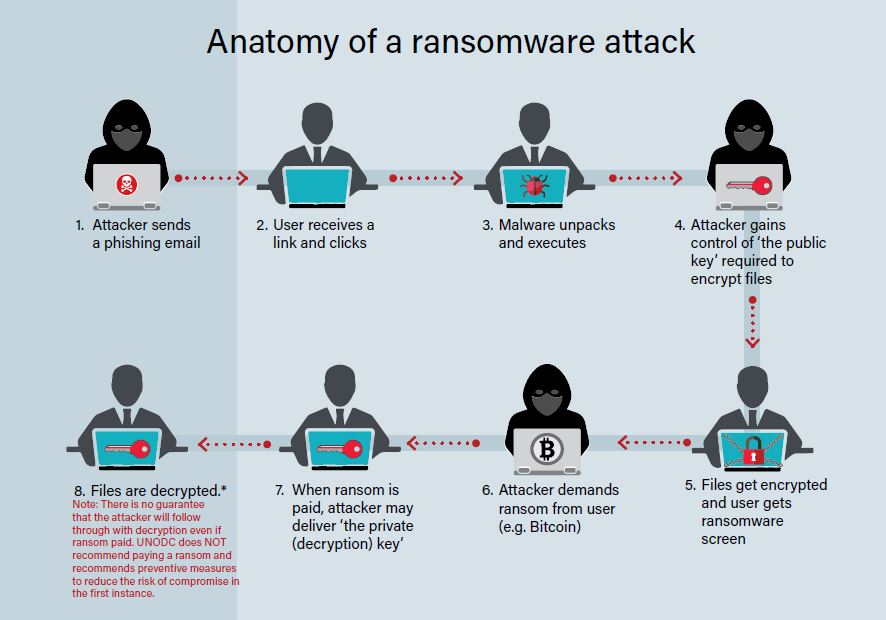
Ransomware attacks have become a significant threat to individuals, businesses, and organizations worldwide. These malicious attacks involve hackers encrypting important files and demanding payment in exchange for the decryption key. While paying the ransom might seem like the only way to recover the data, the best ransomware protection measures can stop these attacks before they even occur.
Unfortunately, ransomware infections usually don't show themselves until the user sees a notification, either in a window, an app, or a full-screen message, demanding money to regain access to the PC or files. It's crucial to take proactive measures to prevent these attacks and ensure business continuity.
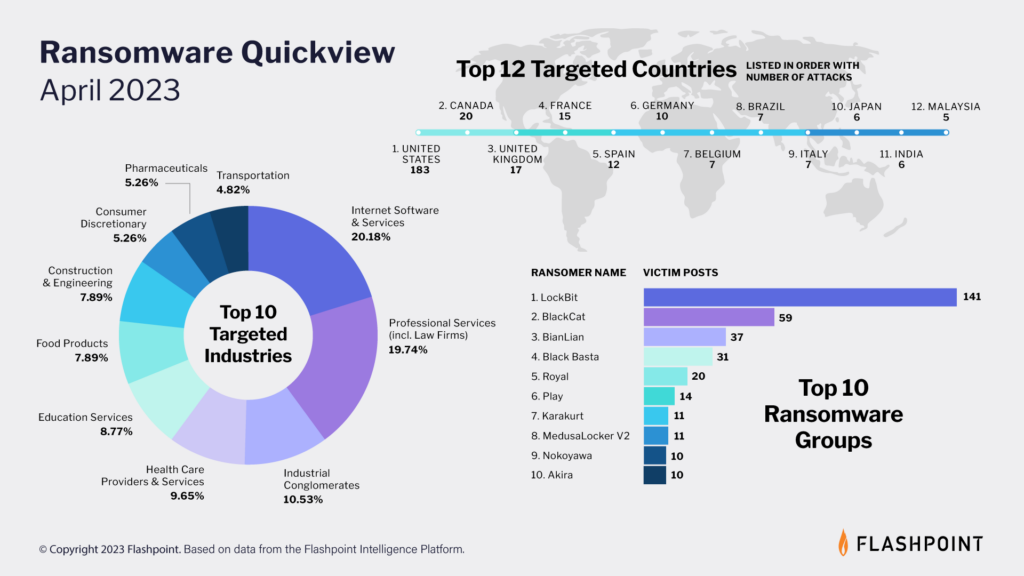
Top 10 Ransomware Families in 2025

This particular example perfectly highlights why Ransomware Threat Protection is so captivating.
According to our white paper, Ransomware Protection and Containment Strategies: Practical Guidance for Endpoint Protection, Hardening, and Containment, the top 10 ransomware families in 2025 are:
- File nmbr32
- DarkTequila
- Code win32="">
- Deanonymizer
- ZeroCleans
- FTE
- Star 0
- RO-Level
- Rotate
- RI578a
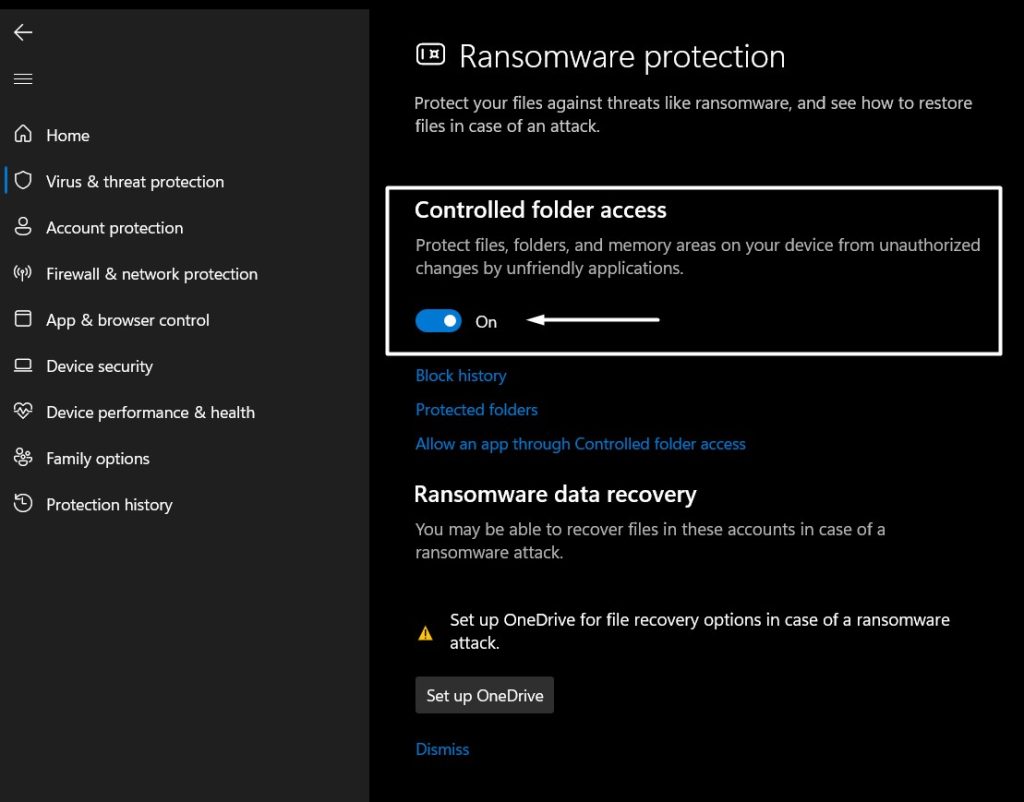
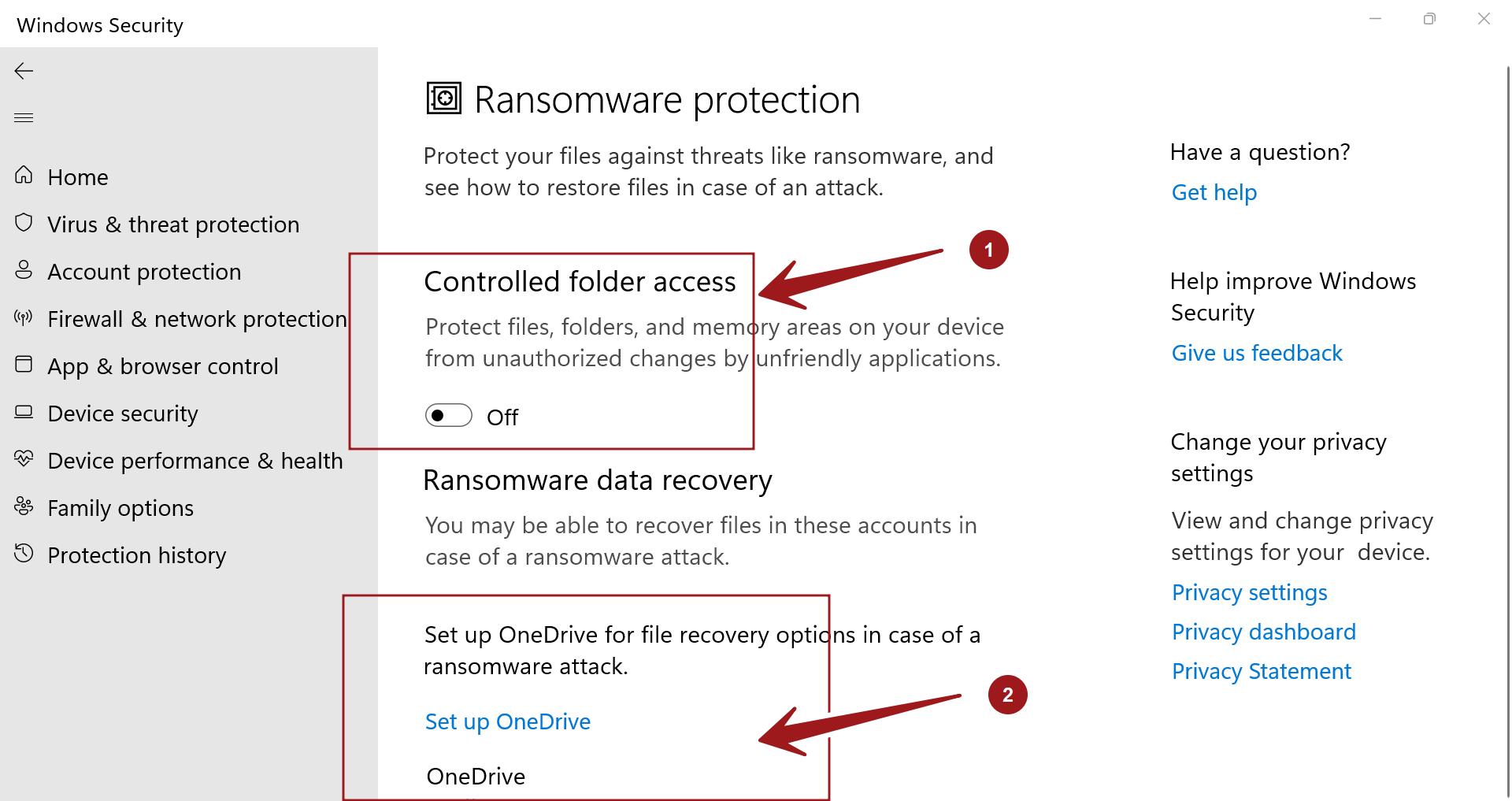
Best Ransomware Protection Solutions
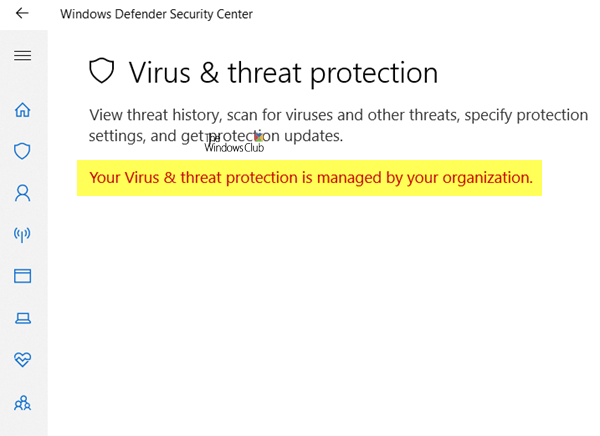
When it comes to preventing ransomware attacks, selecting the right solution is crucial. Some top-rated anti-ransomware tools include:

As we can see from the illustration, Ransomware Threat Protection has many fascinating aspects to explore.
- CrowdStrike Falcon, which provides a unified platform for endpoint protection, including next-gen antivirus (NGAV), Endpoint Detection and Response (EDR), and threat intelligence.
- Kaspersky Anti-Ransomware Tool, which uses cloud-assisted behavior detection to block ransomware and crypto-malware immediately.
- Cynet All-in-One, an advanced threat detection and response platform that provides protection against threats, including ransomware, zero-day attacks, advanced persistent threats (APT), and trojans.
- Sophos Endpoint, which delivers unparalleled defense against advanced cyberattacks with award-winning endpoint protection and control.
Why Ransomware Protection is Essential
With the increasing sophistication of ransomware attacks, it's more crucial than ever to take a proactive approach to prevention and protection. By understanding the threat, selecting the right anti-ransomware solutions, and implementing robust security measures, you can safeguard your organization and protect your critical data.
Conclusion
Remember, prevention is key. Don't wait until it's too late. Take proactive measures today and ensure business continuity tomorrow.