Protecting Data From Ransomware Attacks: A Comprehensive Guide
The Rising Threat of Ransomware Attacks
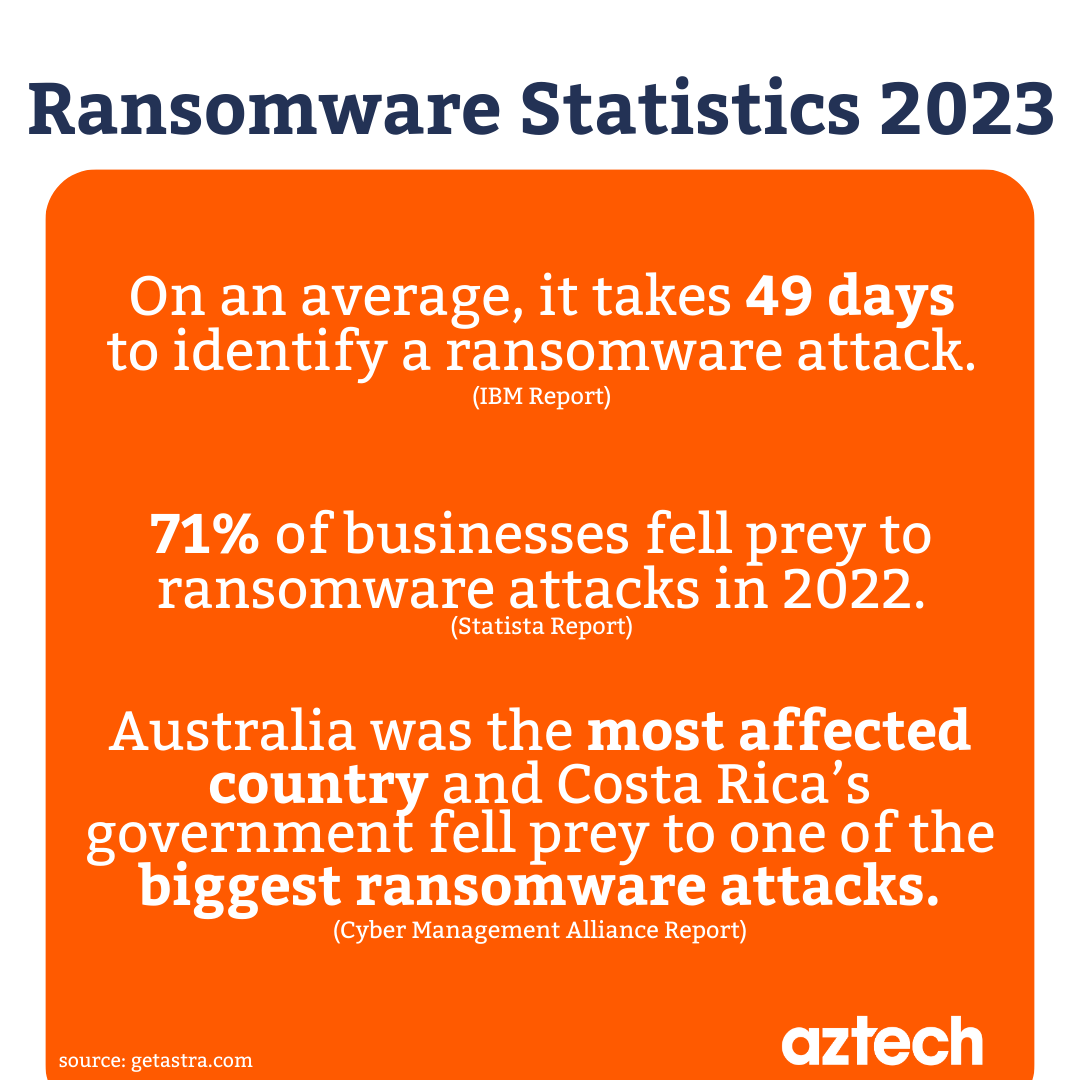
Ransomware attacks have become a significant threat to businesses, hospitals, and individuals worldwide. These malicious attacks encrypt files and data, making them inaccessible until a ransom is paid. The consequences of a ransomware attack can be devastating, resulting in financial losses, reputational damage, and even loss of life. According to the 2025 Data Breach Investigations Report (DBIR) from Verizon, ransomware attacks have surged 49% in 2025, making it essential for organizations to protect their data from these attacks.Understanding Ransomware
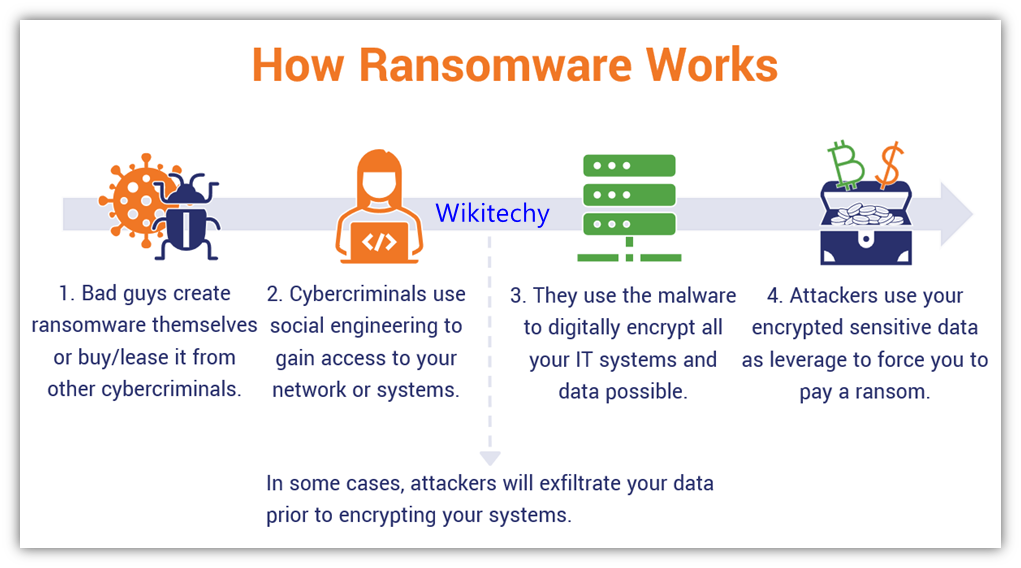
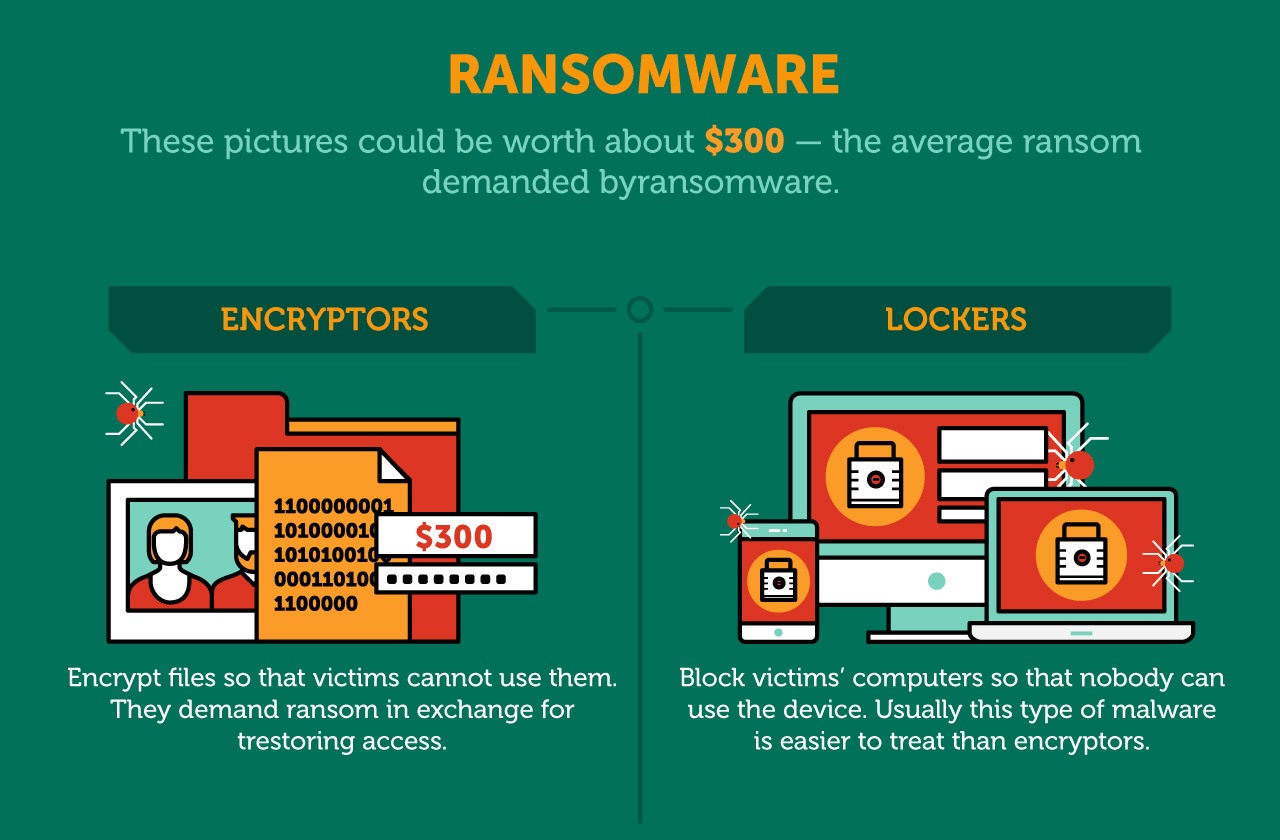
Ransomware is a type of malware that encrypts files and data, making them inaccessible until a ransom is paid. Cybercriminals often use ransomware to extort money from victims, threatening to leak sensitive data or delete files if the ransom is not paid. There are two main types of ransomware: commodity ransomware and human-operated ransomware. Commodity ransomware spreads like a virus, while human-operated ransomware requires active involvement from cybercriminals.Preventing Ransomware Attacks
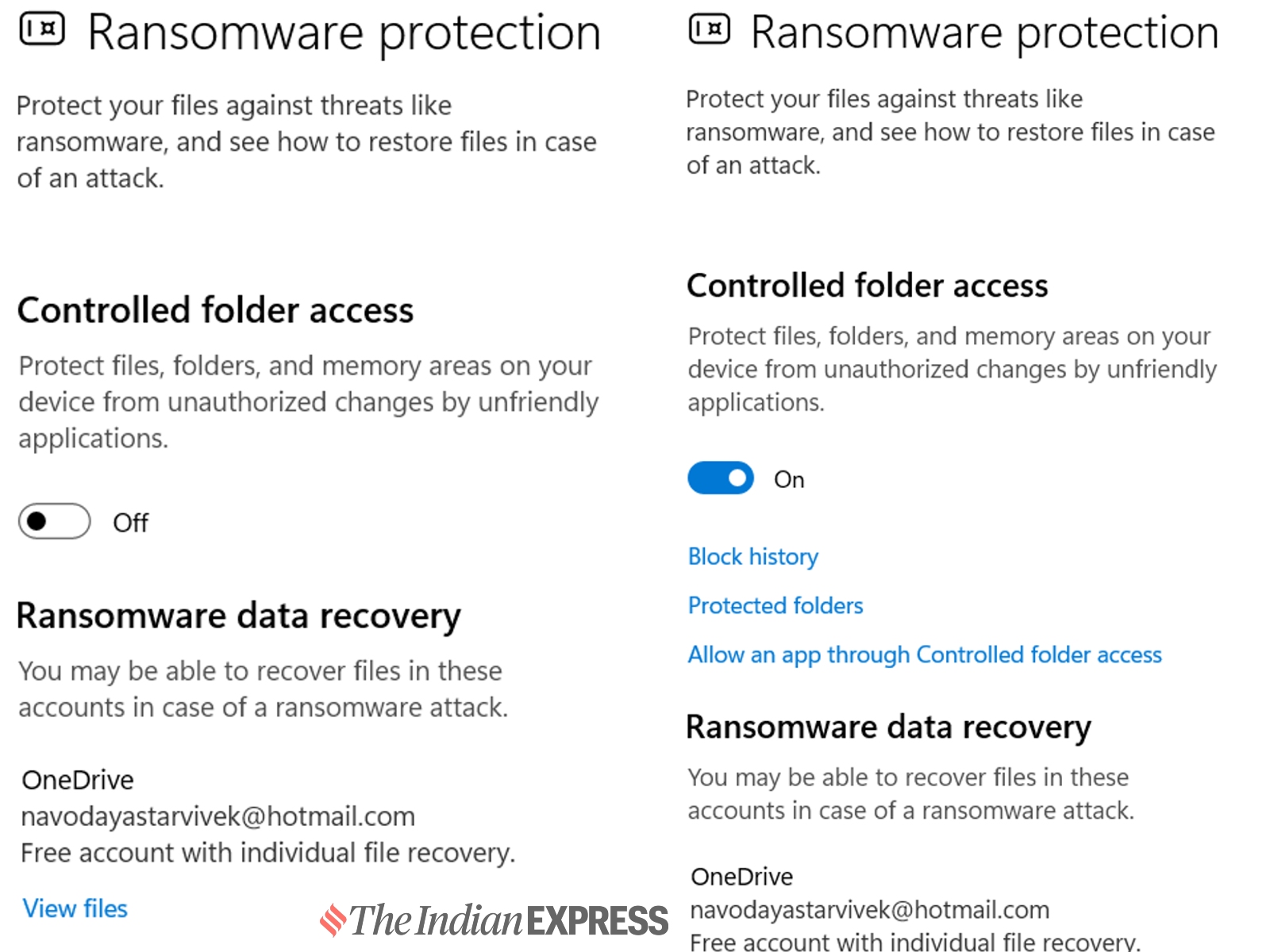
Preventing ransomware attacks requires a proactive approach. Here are some strategies to help protect your data: * Enable delete protection or object lock
Such details provide a deeper understanding and appreciation for Protecting Data From Ransomware Attacks.
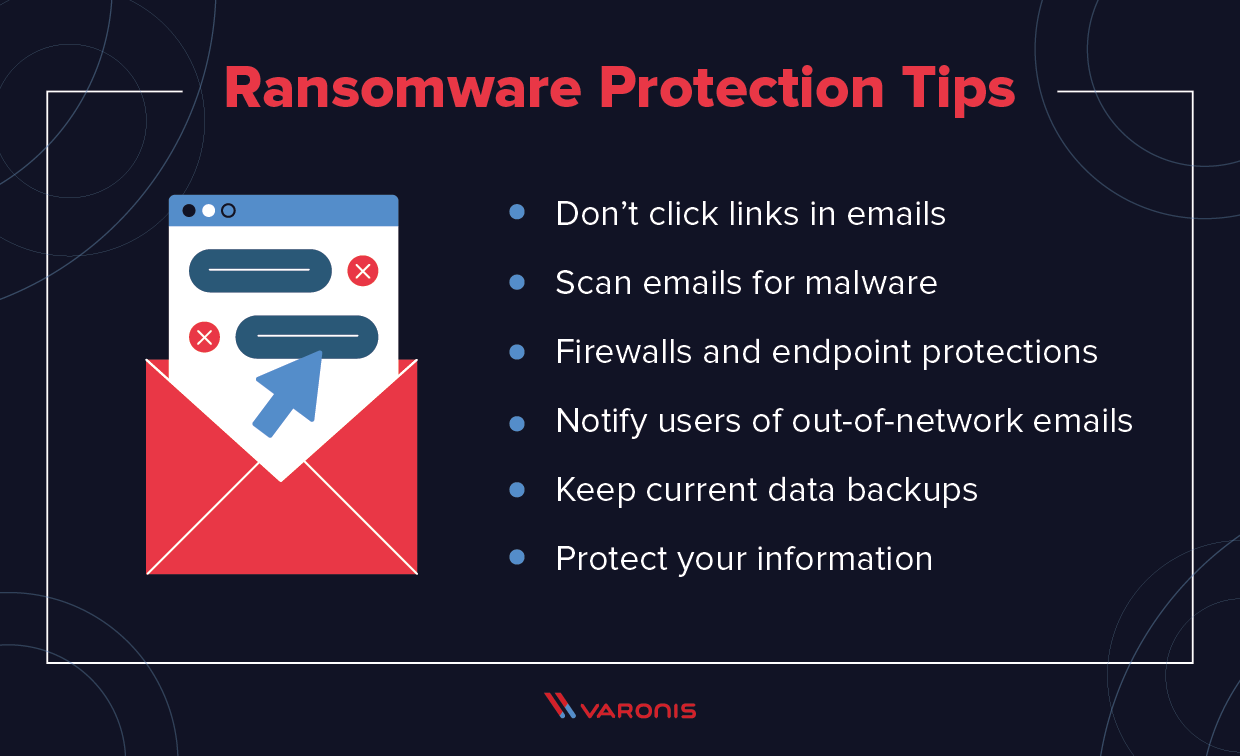
: This feature prevents data from being deleted or overwritten, making it difficult for ransomware to spread. * Regular software updates: Keep your operating system, software, and security patches up to date to prevent vulnerabilities from being exploited. * Frequent data backups: Regularly back up your data to a secure location, such as an external hard drive or cloud storage. * User email security training: Educate users on how to identify and avoid phishing emails that can lead to ransomware attacks. * Implement network segmentation
Such details provide a deeper understanding and appreciation for Protecting Data From Ransomware Attacks.
: Segregate your network into smaller segments to prevent the spread of ransomware in case of an attack.Responding to Ransomware Attacks
If a ransomware attack occurs, responding quickly and effectively is crucial to minimize the damage. Here are some steps to take: * Isolate the affected system: Disconnect the affected system from the network to prevent the spread of ransomware. * Restore data from backups: Use backups to restore your data to a previous state before the attack. * Report the incident