Strengthening Network Security with the G Network Security Setup for Identity and Access Management
Protecting Your Digital Landscape with Identity and Access Management
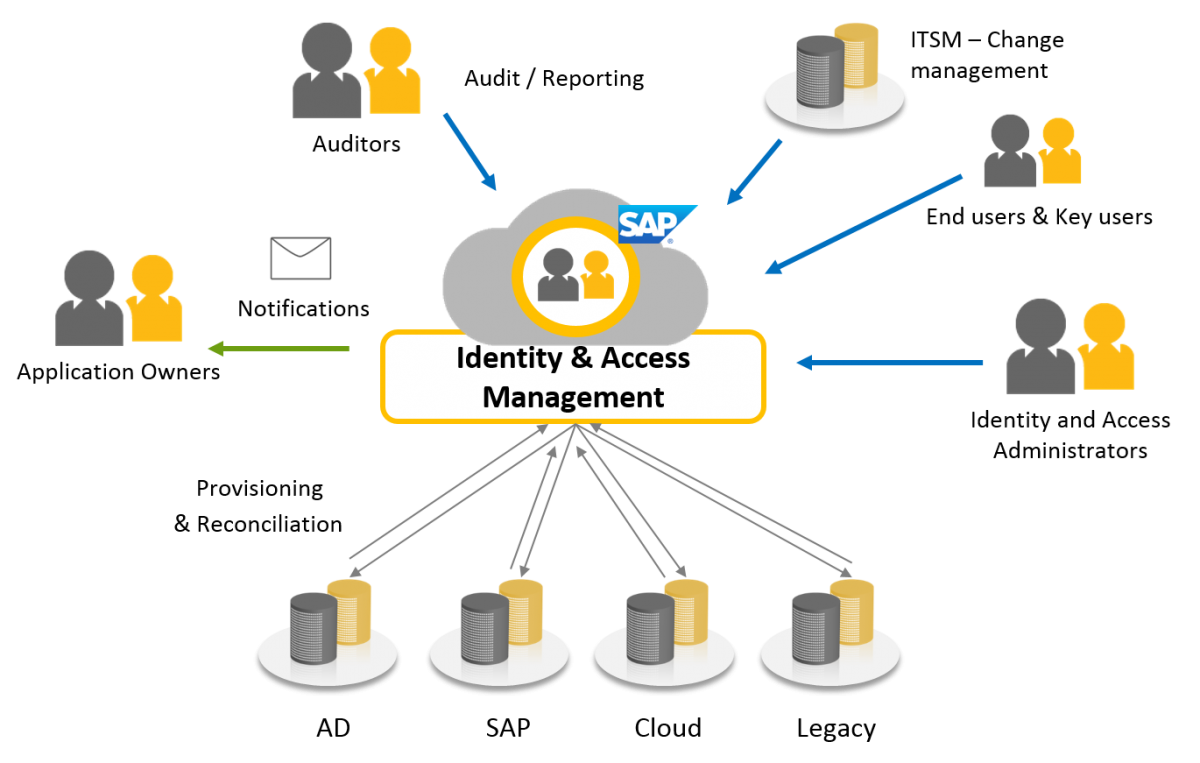
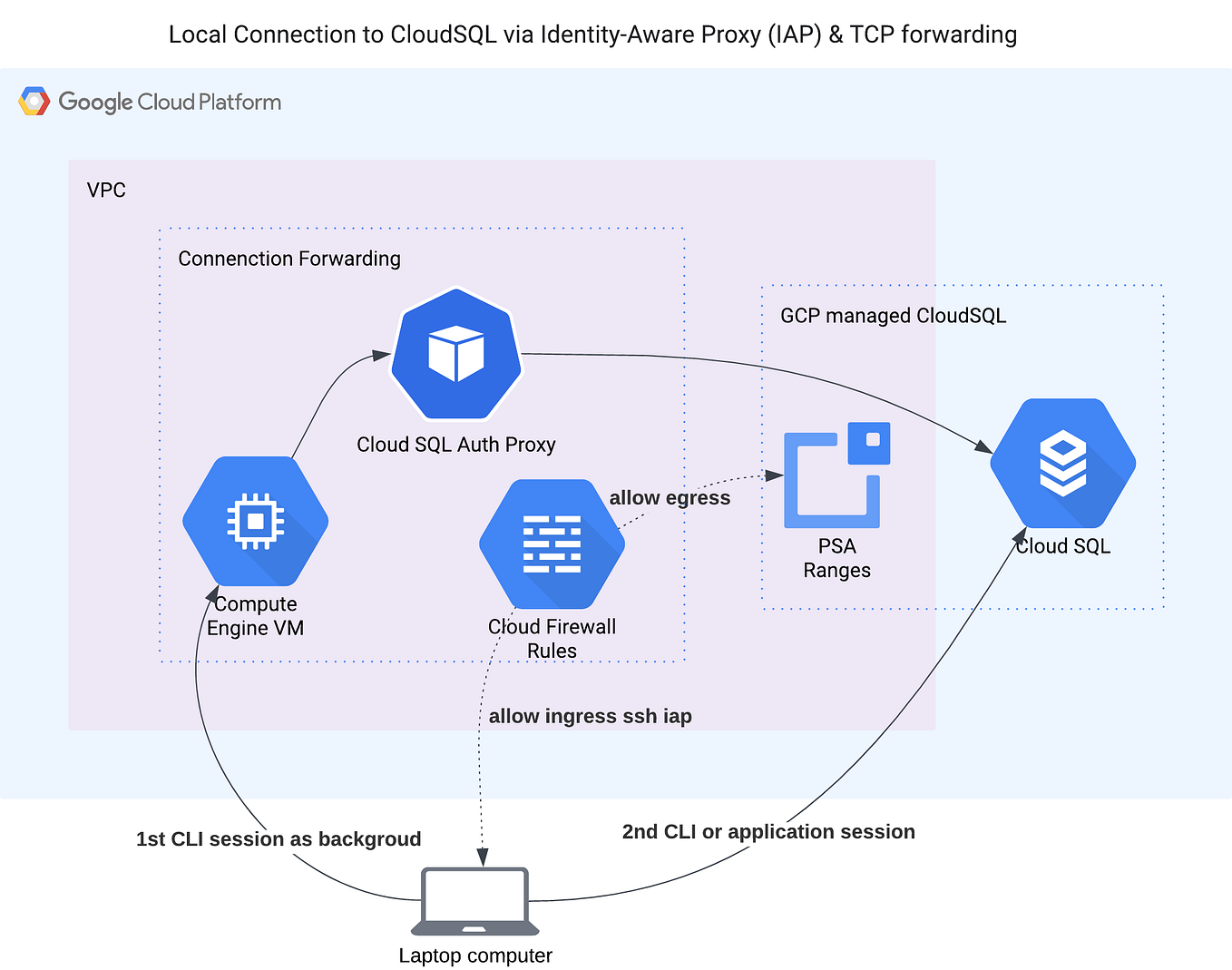
In today's digital era, managing security and access is crucial to safeguarding your assets and maintaining the integrity of your network. The G Network Security Setup for Identity and Access Management (IAM) plays a vital role in this process. It provides a comprehensive framework for managing digital identities and access control, ensuring that only authorized individuals and systems can access sensitive information and resources. By implementing the G Network Security Setup, you can enhance your network's security posture, streamline access control, and minimize the risk of cyber threats.The Importance of Identity and Access Management
Moving forward, it's essential to keep these visual contexts in mind when discussing G Network Security Setup For Identity And Access Management.
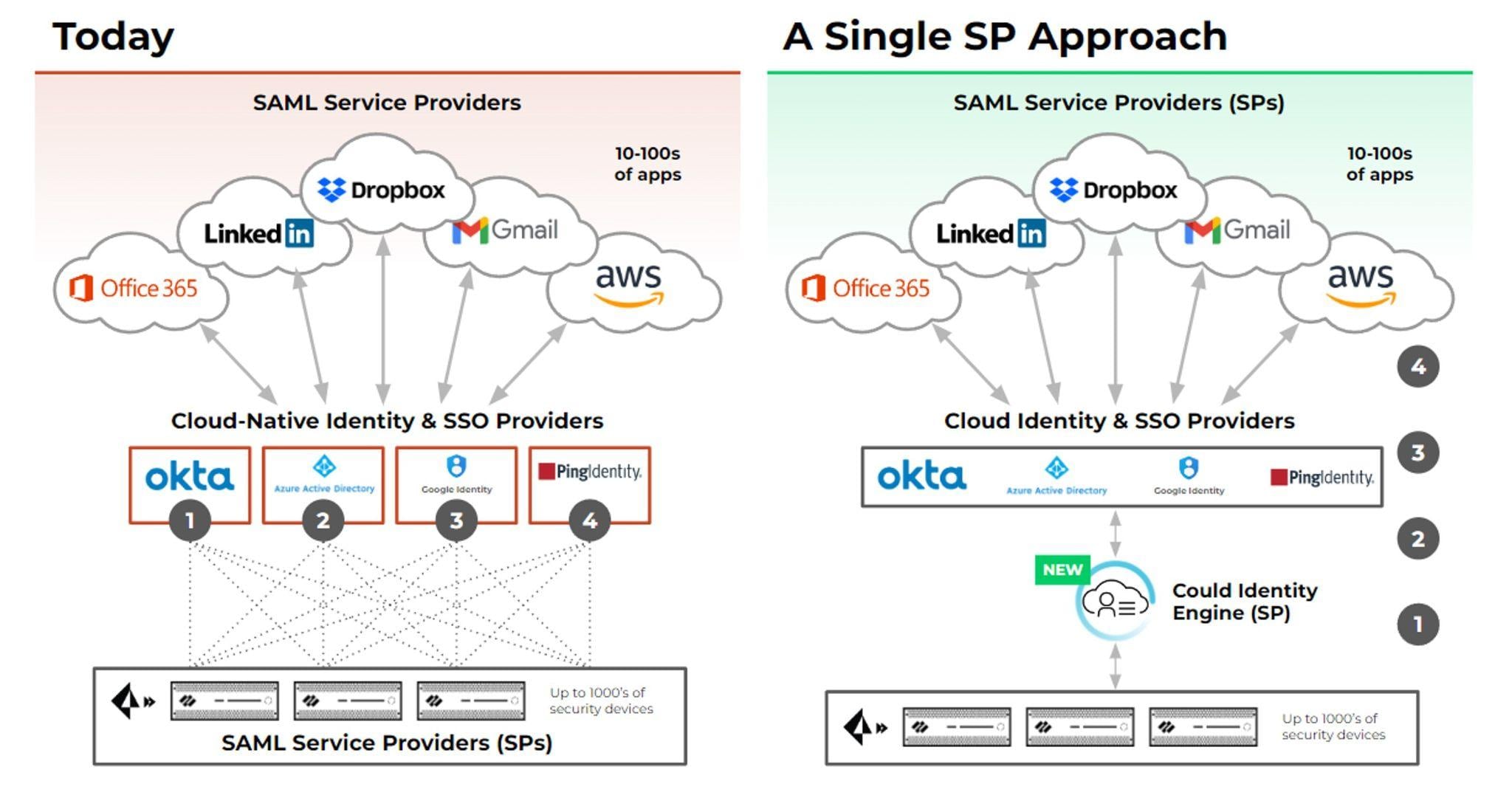
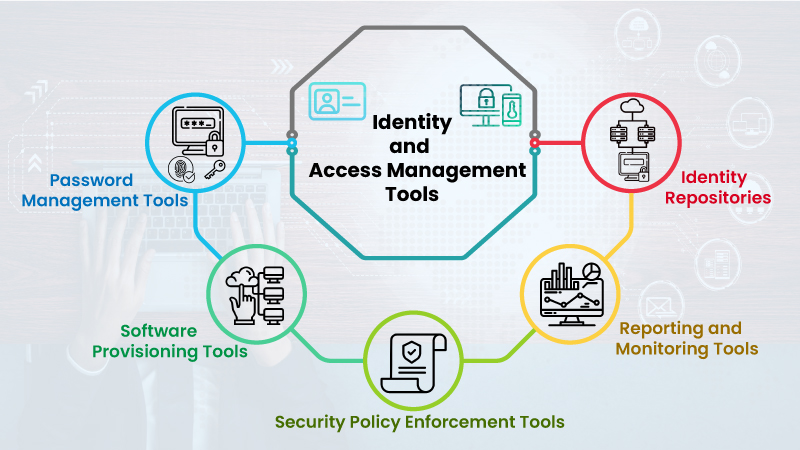
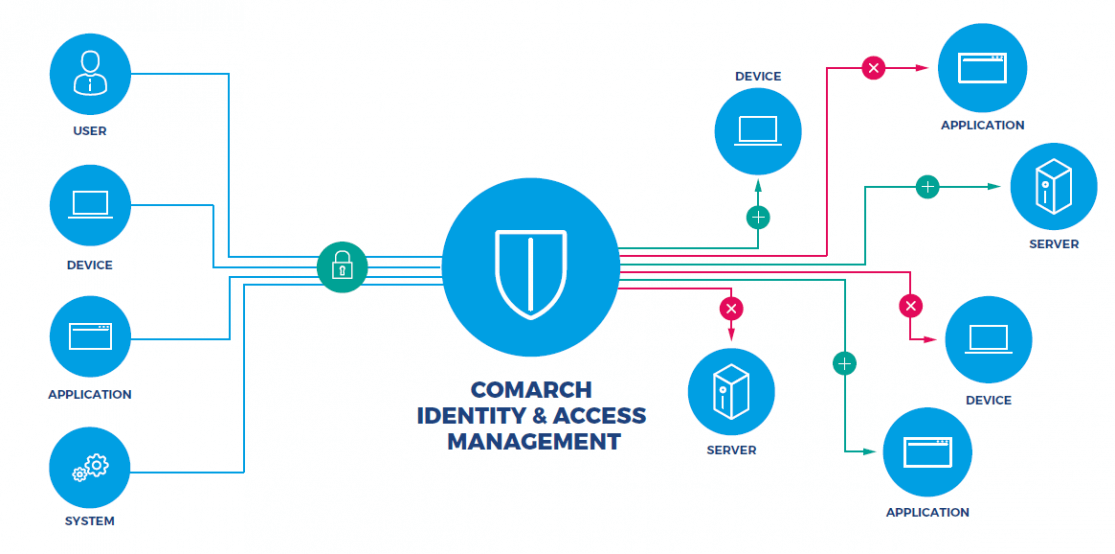
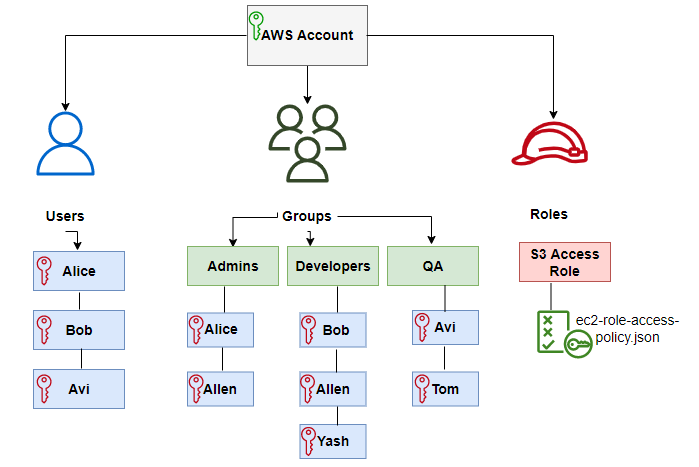
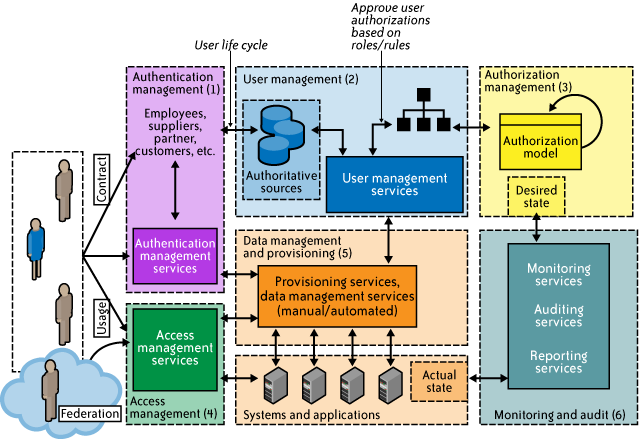
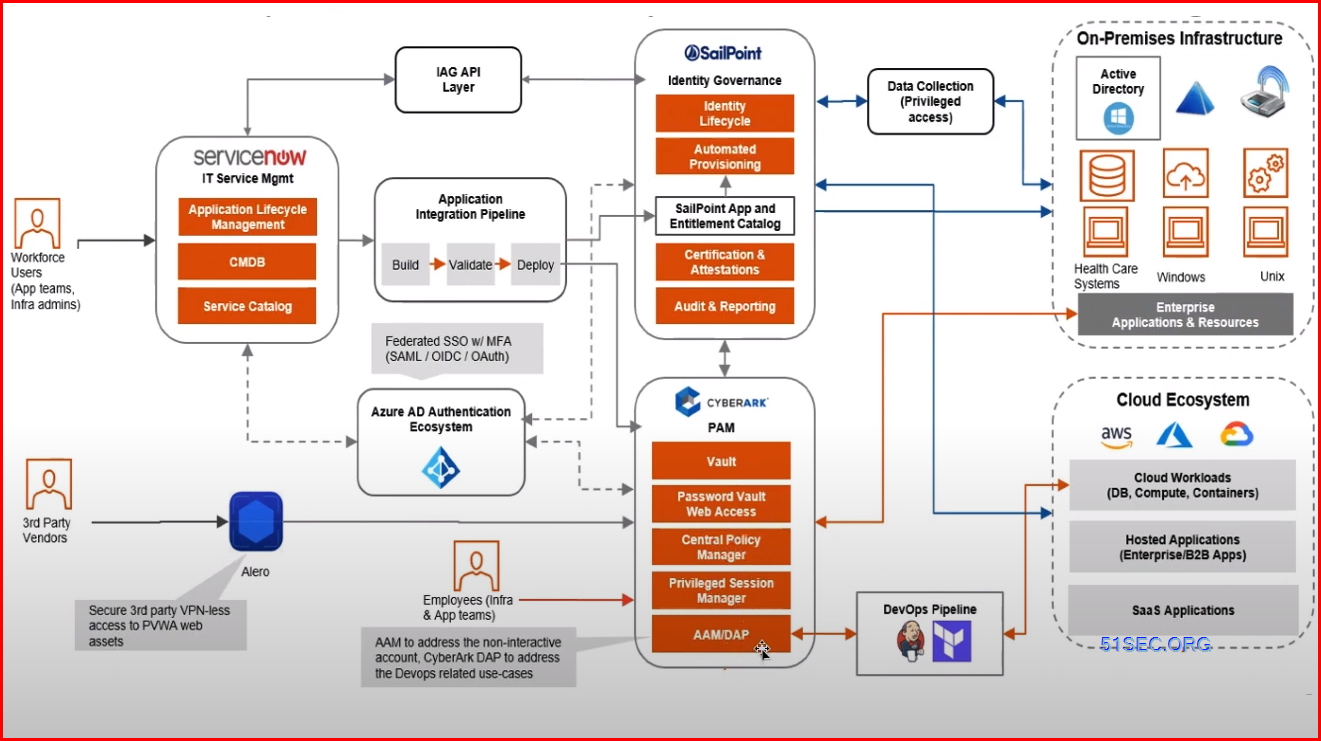
Identity and Access Management (IAM) is a critical component of network security. It enables you to create and manage permissions for Google Cloud resources, unify access control across multiple services, and present a consistent set of operations. With IAM, you can define user roles and access privileges, granting the right level of access to enterprise resources. This approach helps to prevent unauthorized access, confidential data breaches, and other security threats.Key Components of the G Network Security Setup for Identity and Access Management
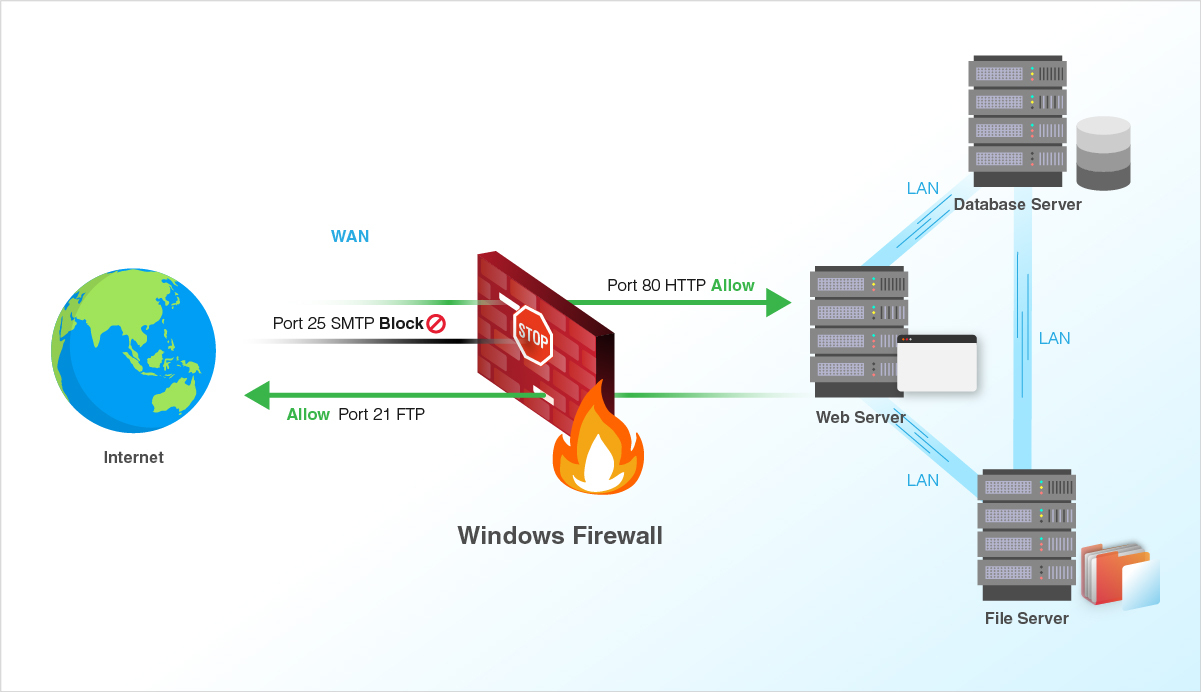
To establish a robust G Network Security Setup for IAM, you'll need to consider the following key components:-
Identity and Access Management (IAM)Services
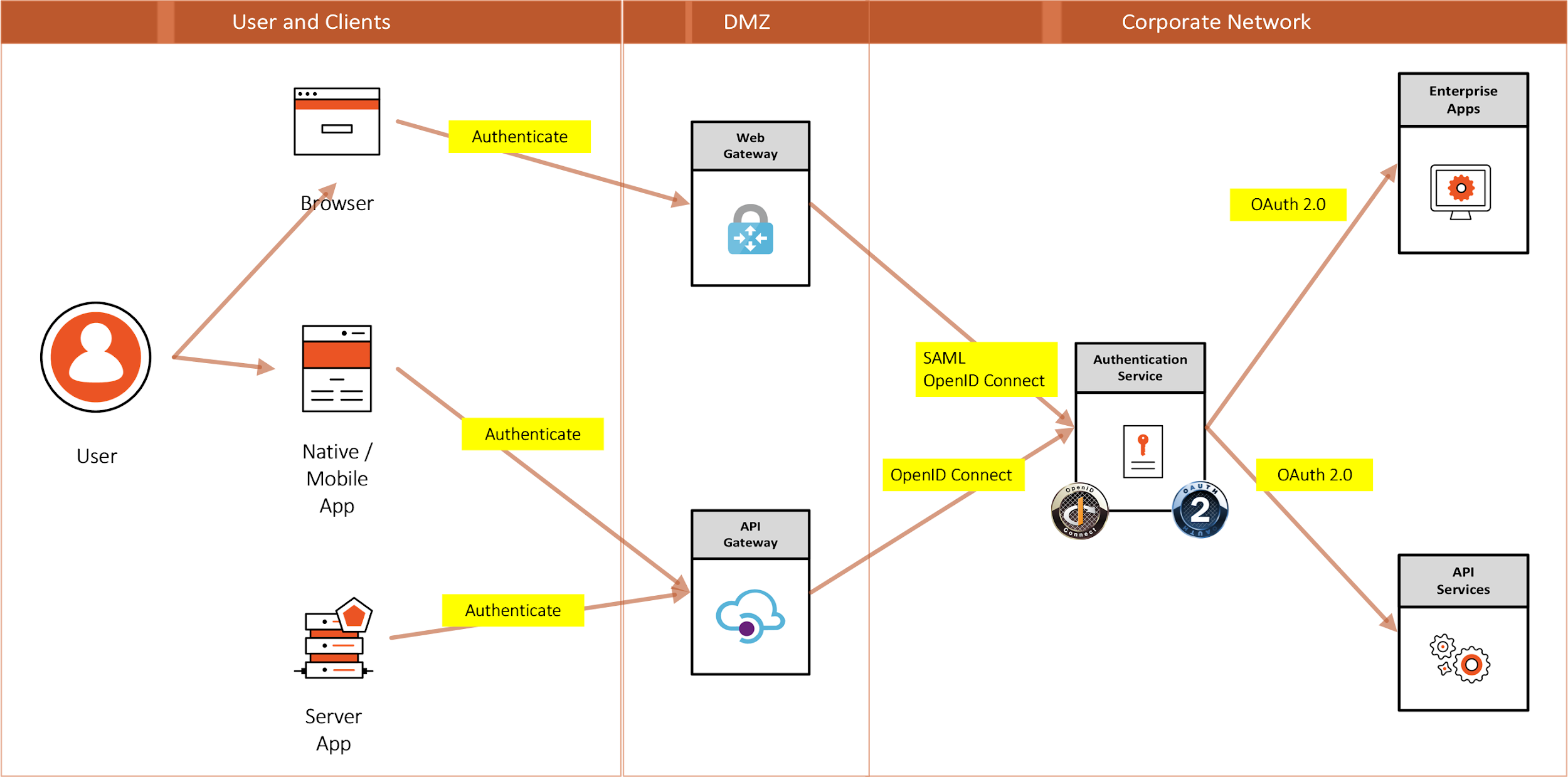
Google Cloud's IAM provides a unified system for managing access control, identities, and permissions across multiple services.
-
Service Accounts
Service accounts belong to projects and play a crucial role in identity management, allowing you to authenticate and authorize applications and services.
-
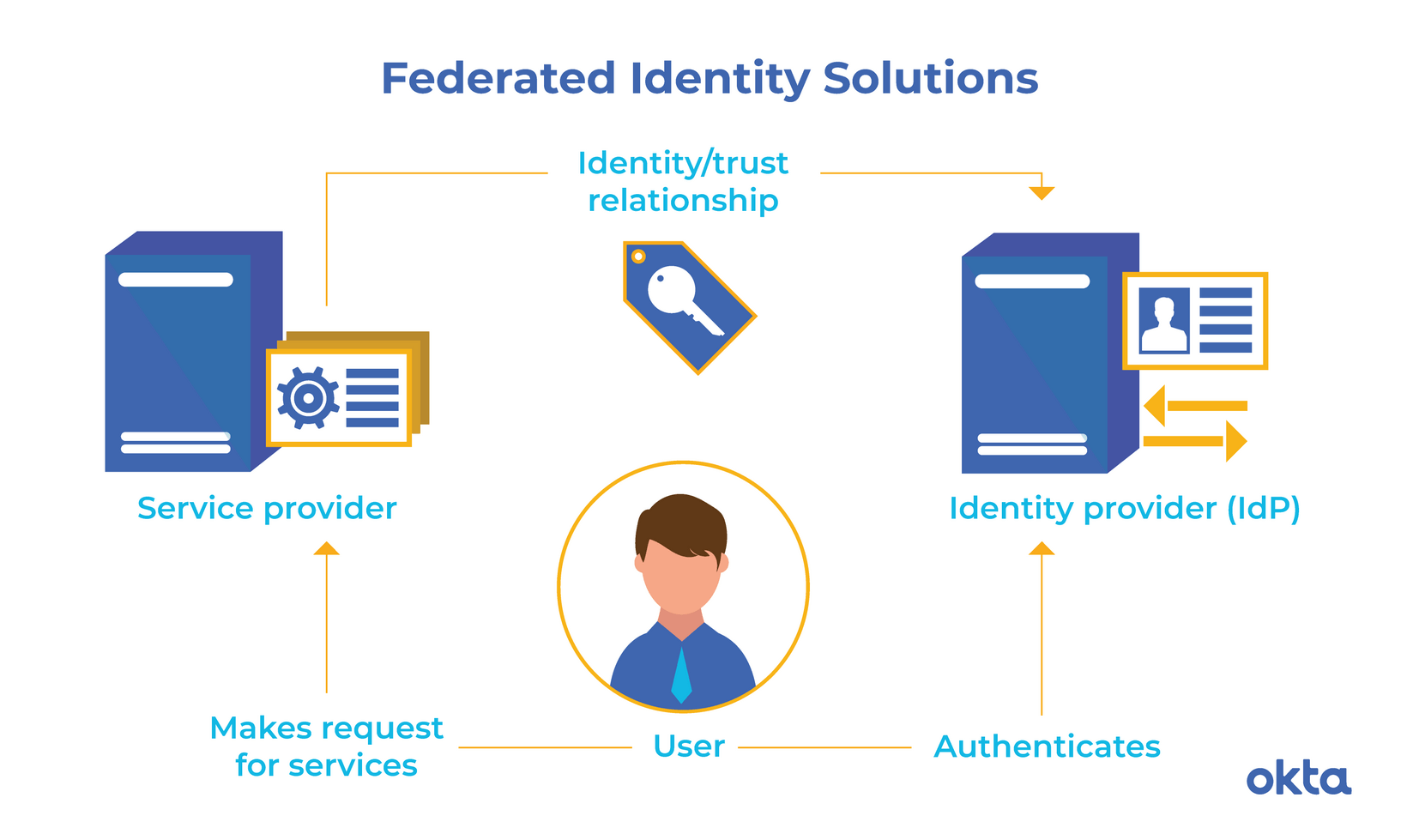
Workload Identity Federation
Workload Identity Federation enables you to use IAM to grant IAM roles to principals that are based on federated identities in a workload identity pool, eliminating the maintenance and security burden of service account keys.
-
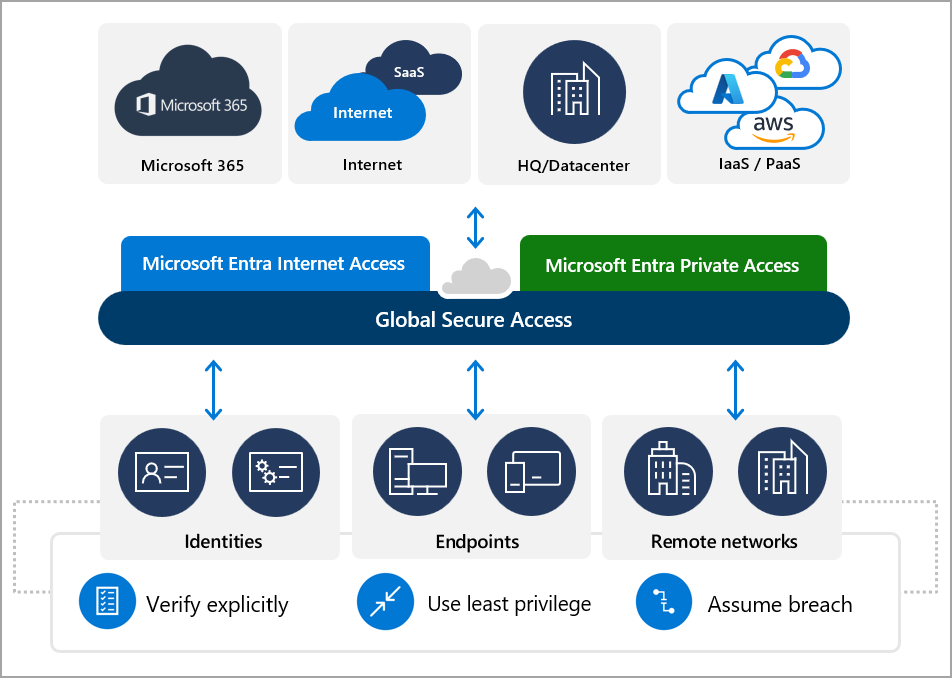
Cloud Security
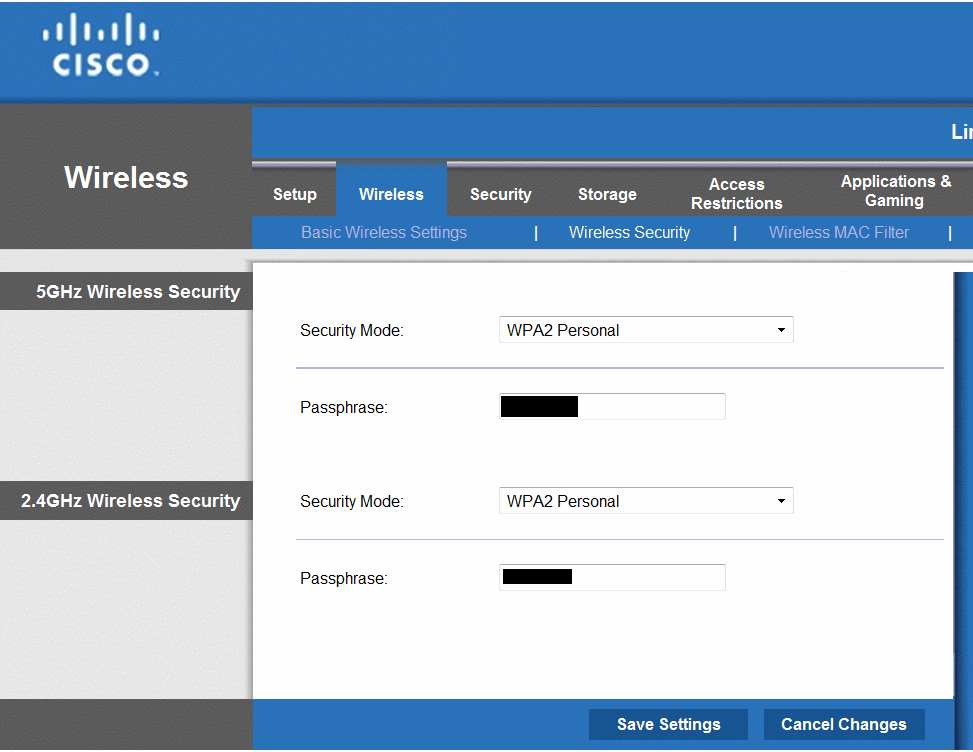
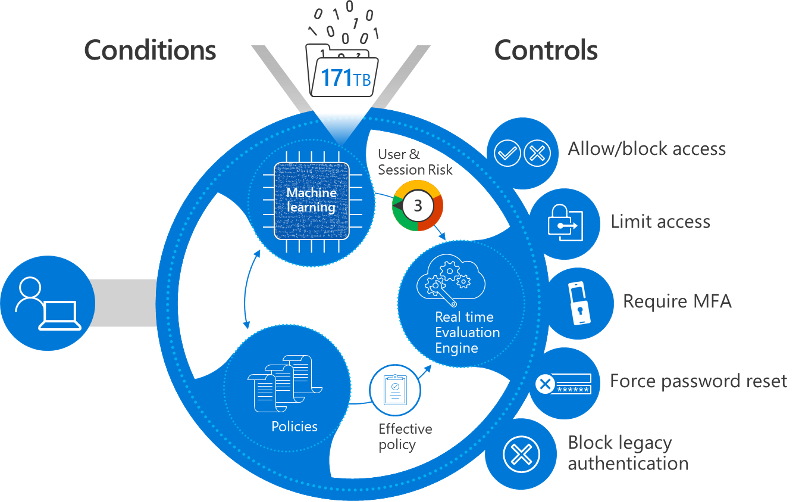
Azure offers a comprehensive security solution that includes threat detection, vulnerability assessment, and policy-based access control to protect your network and data.
-
Cloud Identity and Access Management (CIAM)
A cloud-based CIAM platform allows you to add identity and access management functionality to your app, protect user accounts, and scale with confidence.
Benefits of the G Network Security Setup for Identity and Access Management
The G Network Security Setup for Identity and Access Management offers several benefits, including:-
Improved Security Posture
Implementing the G Network Security Setup for IAM enhances your network's security posture by preventing unauthorized access and confidential data breaches.
-
Streamlined Access Control
The G Network Security Setup for IAM simplifies access control by providing a unified system for managing identities and permissions across multiple services.
-
Enhanced Compliance
The G Network Security Setup for IAM helps you maintain compliance with regulatory requirements by providing a robust access control framework.
-
Reduced Risk of Cyber Threats
The G Network Security Setup for IAM minimizes the risk of cyber threats by controlling access to sensitive information and resources.












_Magic-Quadrant-for-Privileged-Access-Management--Lead.jpeg)